**Note:** Please log in to your CrowdStrike portal and download the latest TCC profiles. The screenshots below are provided for reference if you choose to create the TCC profiles manually.
Falcon Configuration Profile for Sonoma and earlier:| **Security & Privacy Payload:** - Bundle ID: - com.crowdstrike.falcon.Agent - com.crowdstrike.falcon.App - Code requirement: - identifier "com.crowdstrike.falcon.Agent" and anchor apple generic and certificate 1\[field.1.2.840.113635.100.6.2.6\] /\* exists \*/ and certificate leaf\[field.1.2.840.113635.100.6.1.13\] /\* exists \*/ and certificate leaf\[subject.OU\] = X9E956P446 - Access to service: - Full Disk Access | [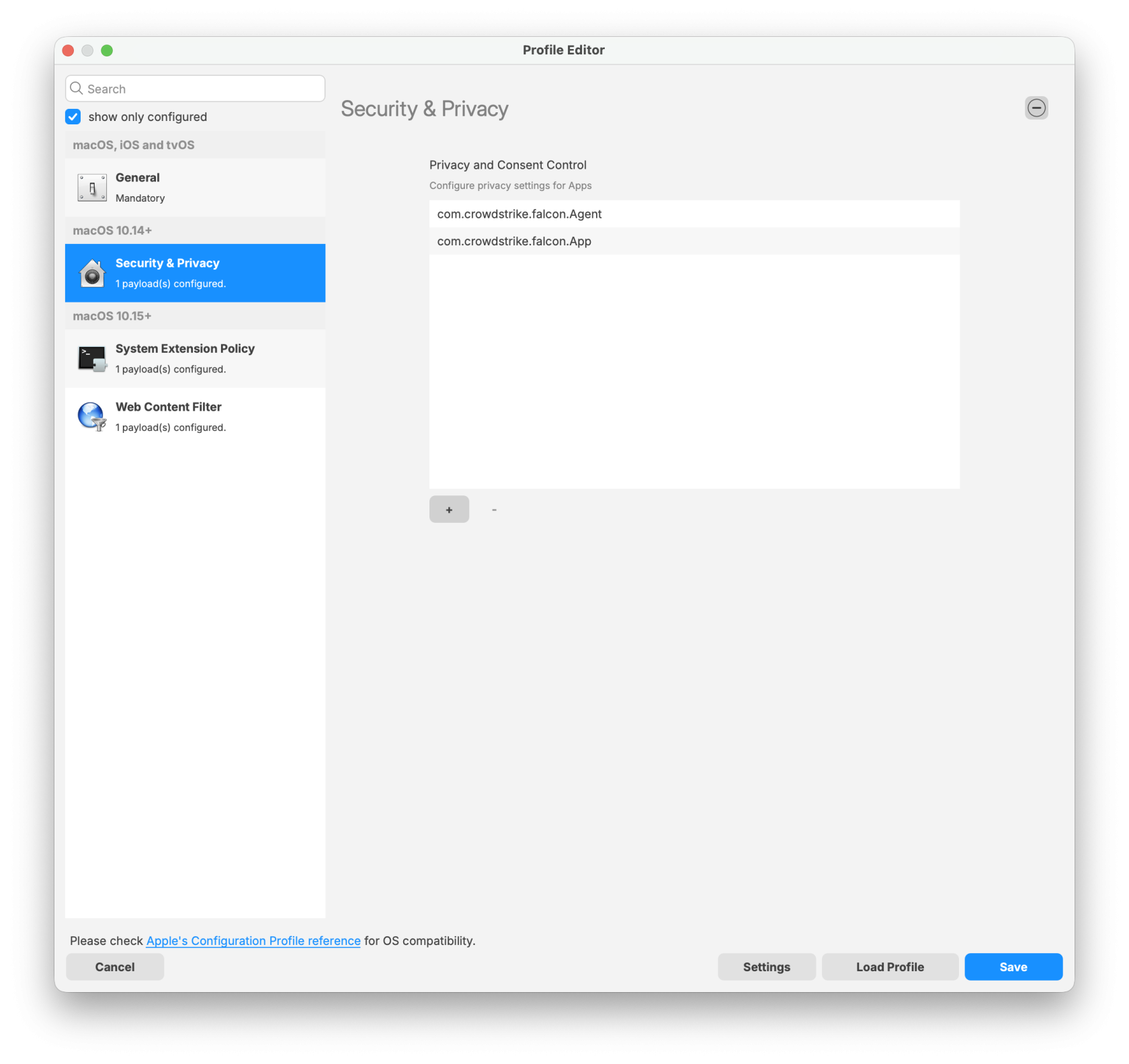](https://kb.filewave.com/uploads/images/gallery/2026-01/VeAguvwWKb3N5EDD-falcon-configuration-profile-for-sonoma-and-earlier0.png) |
| - Agent configuration | [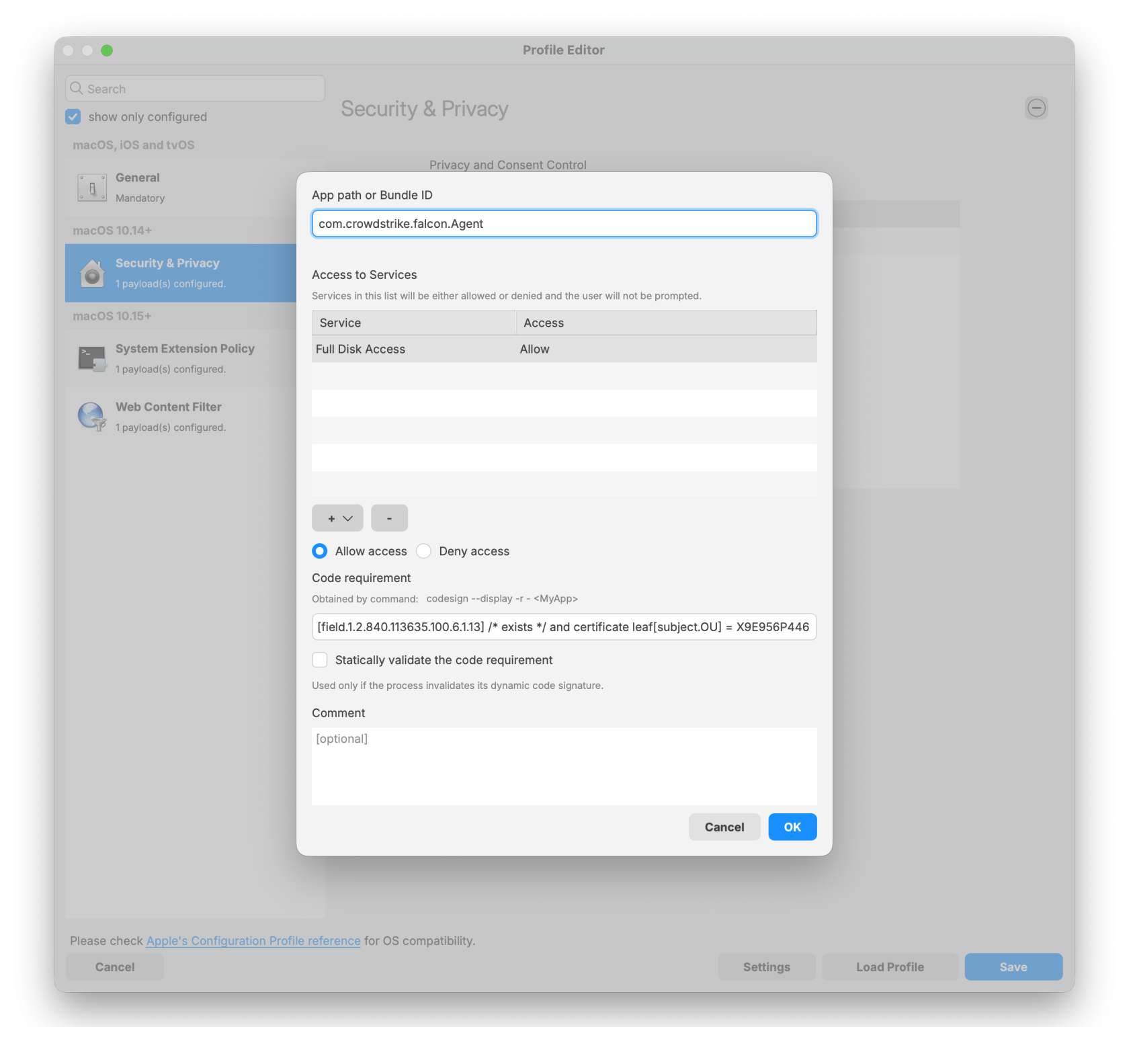](https://kb.filewave.com/uploads/images/gallery/2026-01/xira0rGVgXkX4fu3-agent.png) |
| - App configuration | [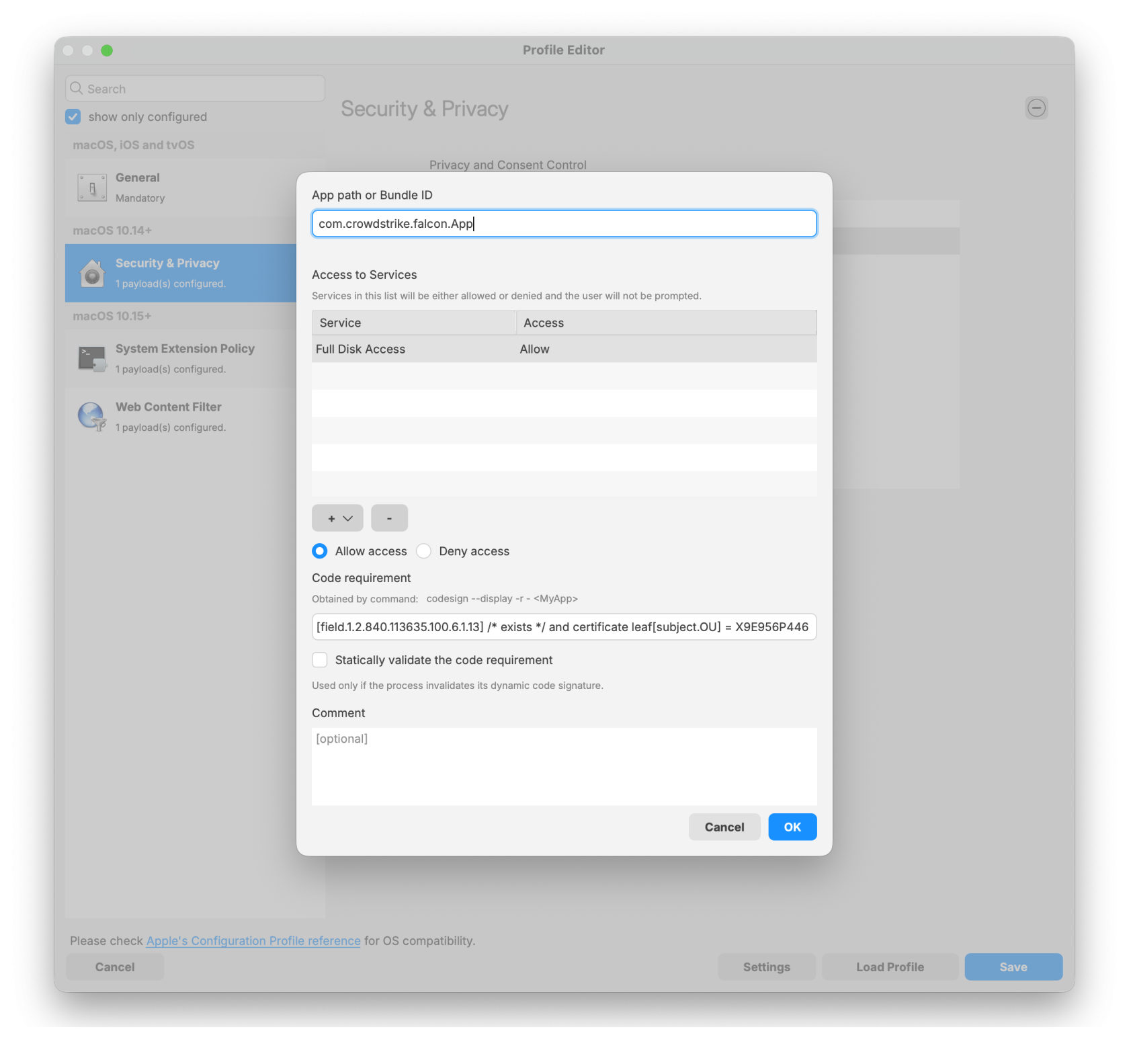](https://kb.filewave.com/uploads/images/gallery/2026-01/CsEm4mpYjMi28rCq-app.png) |
| **System Extension Policy Payload:** - Check box 'Can approve additional system extensions' - Allowed Team Identifiers: - X9E956P446 - Allowed System Extensions - com.crowdstrike.falcon.Agent - Allowed System Extension Types: - Network - Endpoint security | [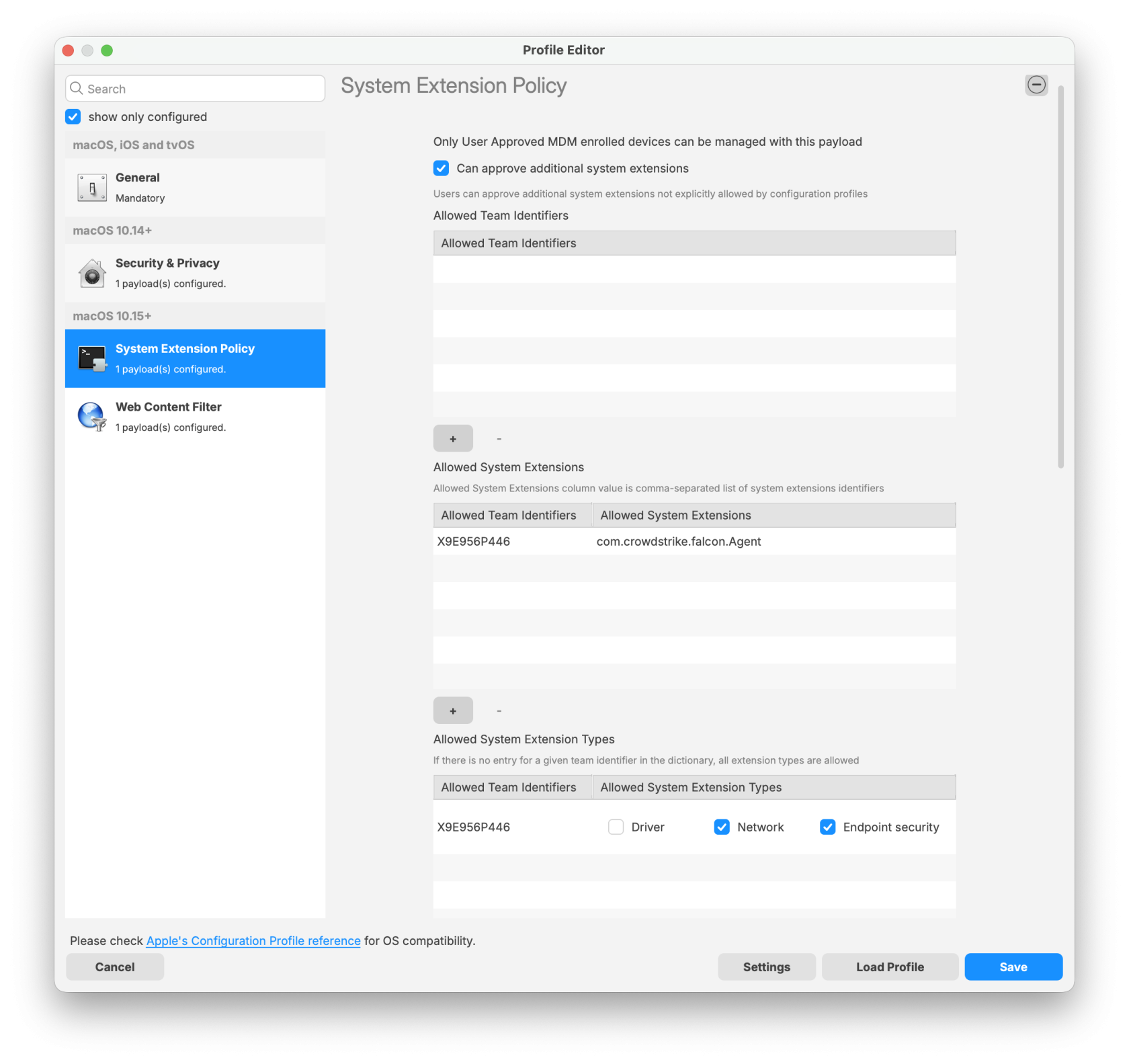](https://kb.filewave.com/uploads/images/gallery/2026-01/svMgQ95jWKmAiTGm-falcon-configuration-profile-for-sonoma-and-earlier1.png) |
| **Web Content Filter Payload:** - Name: Falcon - Identifier: com.crowdstrike.falcon.App - Filter Network Traffic - Socket Filter Bundle Identifier: - com.crowdstrike.falcon.Agent - Socket Filter Designated Requirement: - identifier "com.crowdstrike.falcon.Agent" and anchor apple generic and certificate 1\[field.1.2.840.113635.100.6.2.6\] and certificate leaf\[field.1.2.840.113635.100.6.1.13\] and certificate leaf\[subject.OU\] = "X9E956P446" | [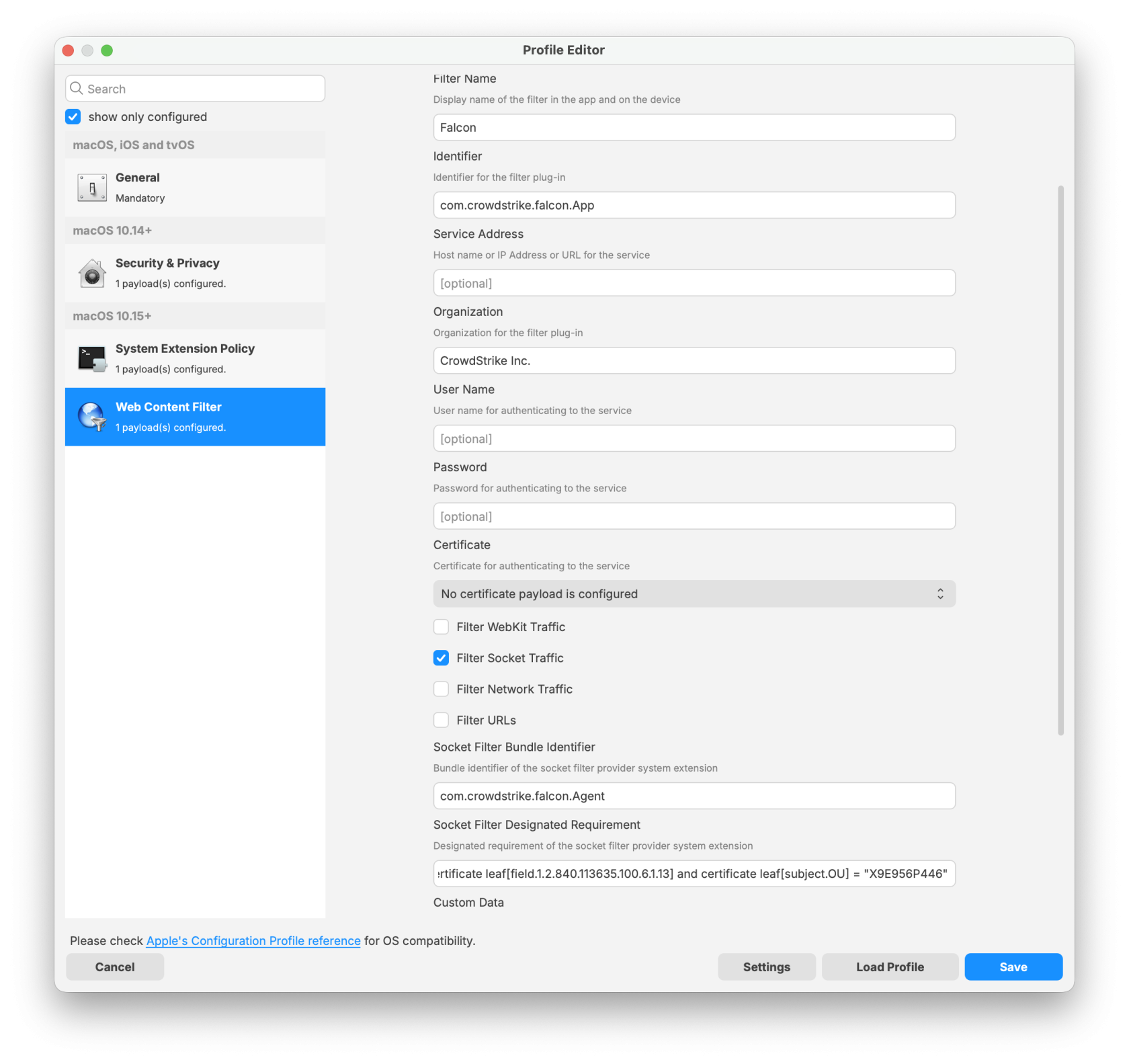](https://kb.filewave.com/uploads/images/gallery/2026-01/plA53wMwJbY0UA1x-falcon-configuration-profile-for-sonoma-and-earlier2.png) |
| **System Extension Policy Payload:** - Team Identifiers: - X9E956P446 - Non Removable From UI System Extensions: - com.crowdstrike.falcon.Agent | [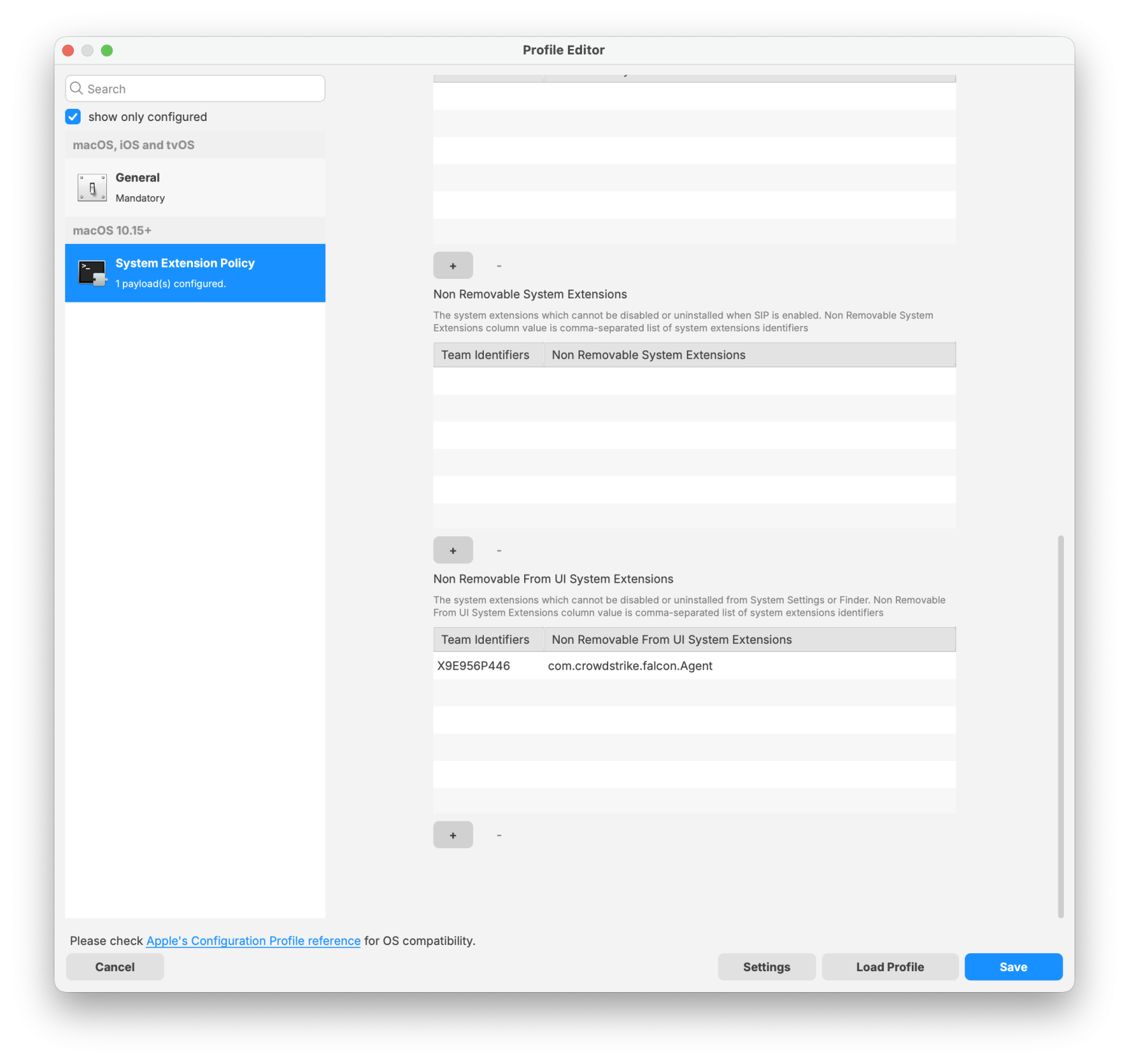](https://kb.filewave.com/uploads/images/gallery/2026-01/6PJA0gxFXERWCDAl-falcon-configuration-profile-update-for-sequoia-and-later0.png) |
**Note:** Please log in to your CrowdStrike portal and download the latest PKG installer to ensure a successful import and deployment. The PKG installer must be used along with the two required scripts: the Requirement script and the Activation script.
[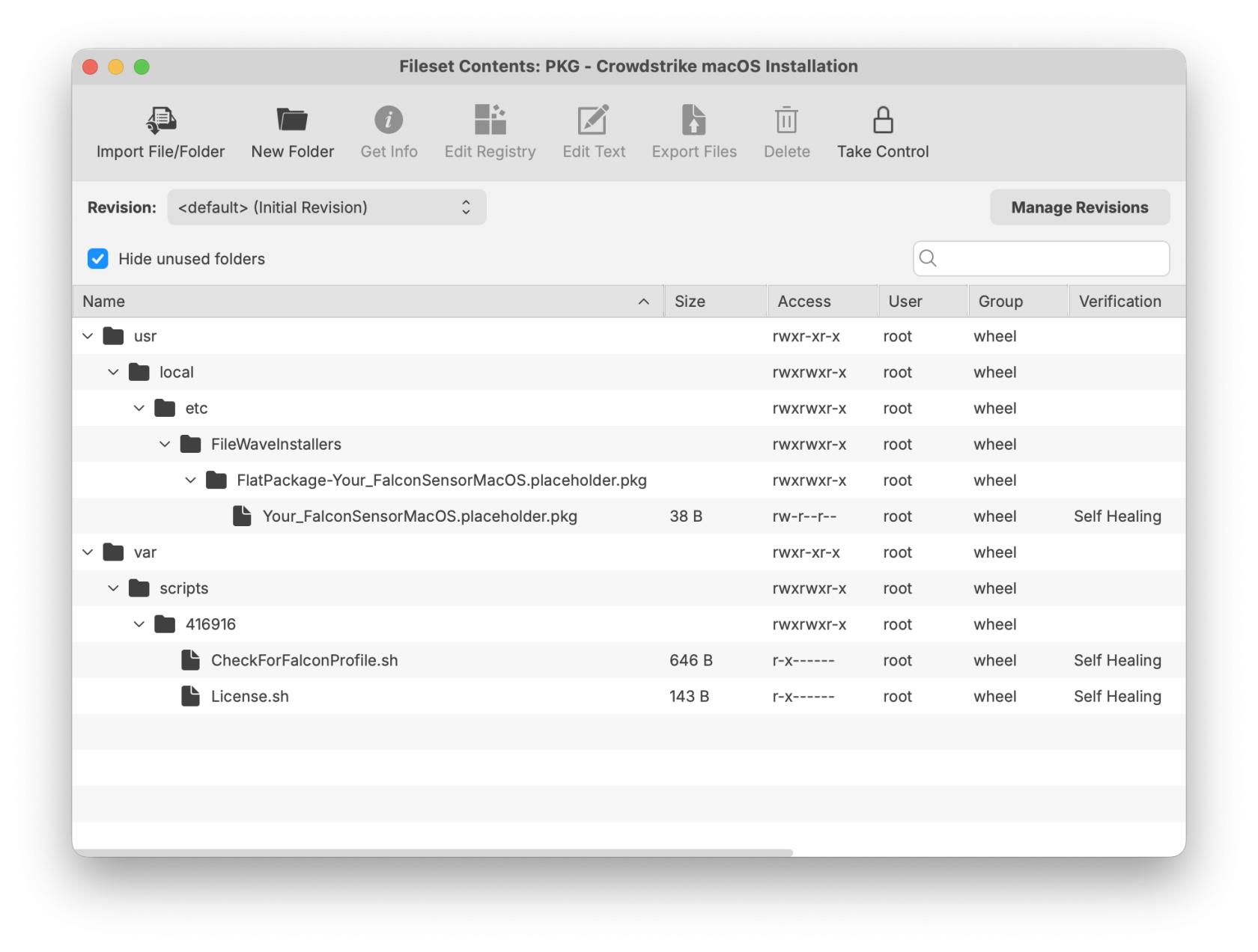](https://kb.filewave.com/uploads/images/gallery/2026-01/MsMkjJvzxFrLZa9z-updatedcrowdstrikemacosinstallation.png) ## CrowdStrike License Customizing the Fileset with your CrowdStrike license is required. The Fileset has a License.sh script to edit and enter in your license code.| #### Editing the License.sh script 1. Highlight your CrowdStrike PKG installer Fileset 2. Select Scripts to open the Script window. 3. Highlight License.sh 4. Click Edit | [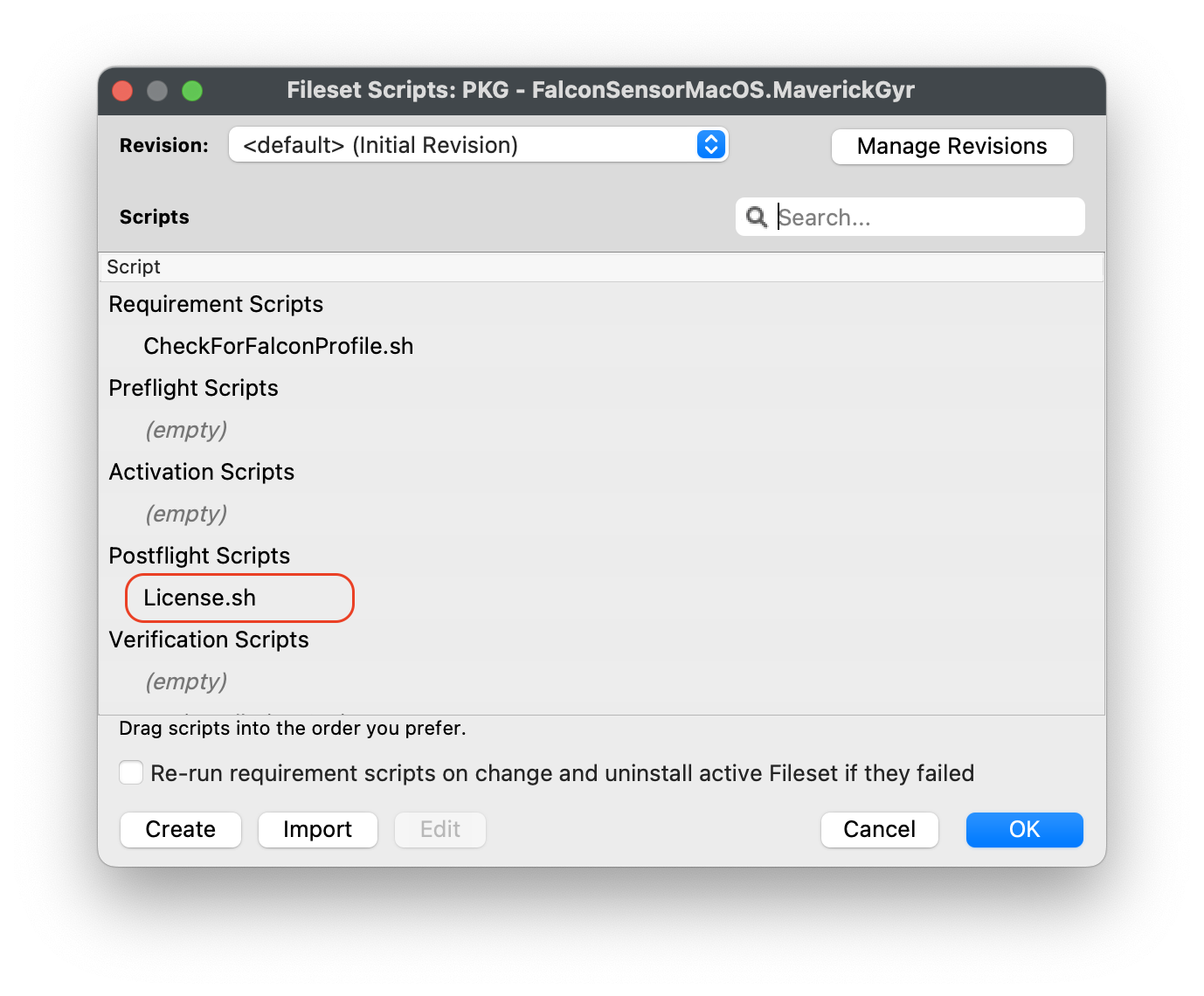](https://kb.filewave.com/uploads/images/gallery/2023-08/pf41UhyqVBanl9qu-crowdstrikescripts1.png) |
| #### Entering in your license code 1. Highlight the ####### string and enter in your CrowdStrike License code 2. Click OK to save 3. Click OK to save again to save your license code for the CrowdStrike Fileset | [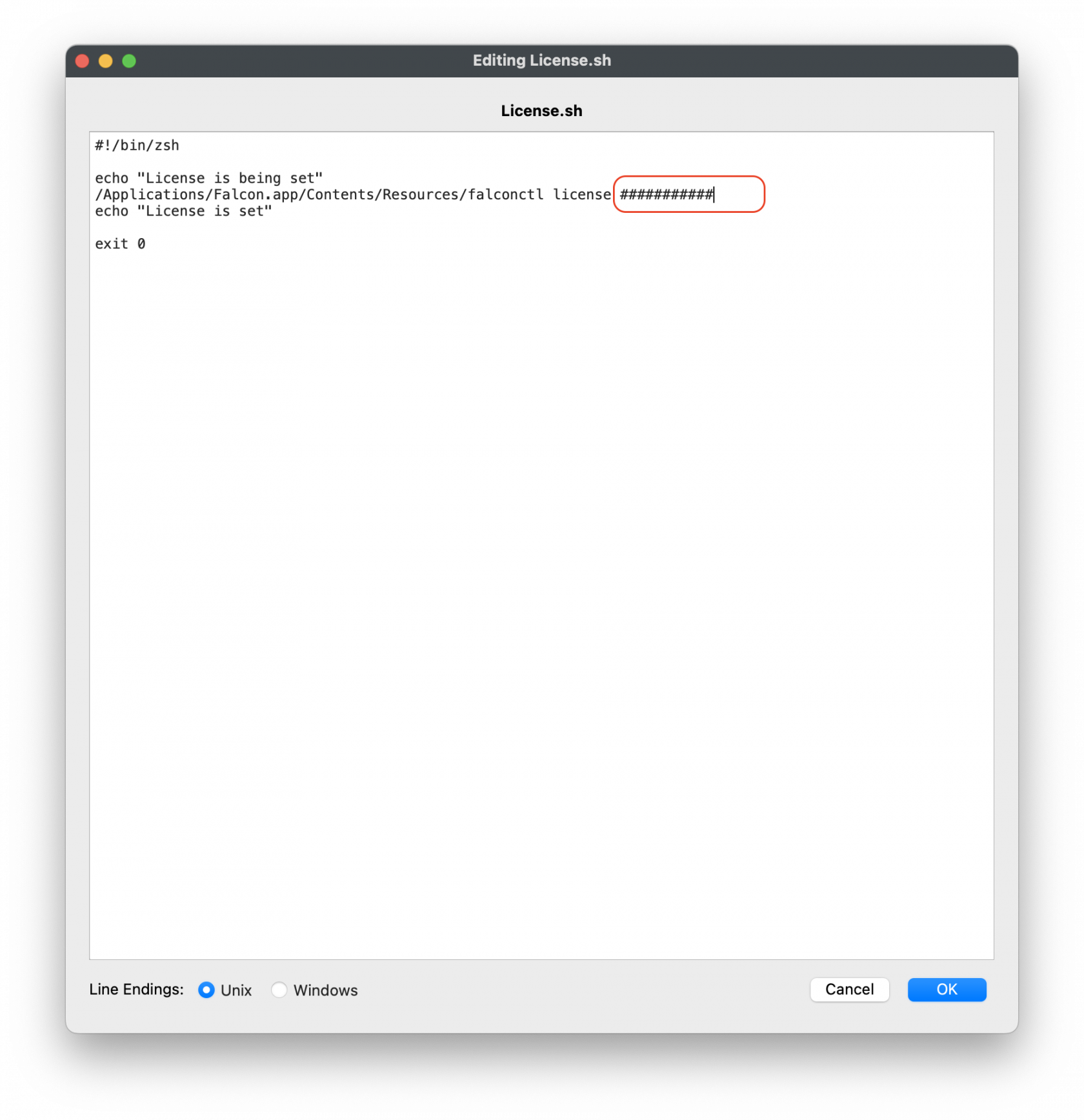](https://kb.filewave.com/uploads/images/gallery/2023-08/mX5Td89pE3hDJXMo-crowdstrikescripts2.png)
License code script``` #!/bin/zsh echo "License is being set" /Applications/Falcon.app/Contents/Resources/falconctl license ########## echo "License is set" exit 0 ``` |
**Note:** The Requirement script verifies that the CrowdStrike Falcon TCC profiles are installed successfully before the CrowdStrike installer runs. The script checks for both profiles and confirms they are installed before proceeding with the CrowdStrike deployment.
| #### Editing the CheckForFalconProfile.sh 1. Highlight your CrowdStrike PKG installer Fileset 2. Select Scripts to open the Scripts window 3. Highlight the CheckForFalconProfile.sh script 4. Click Edit | [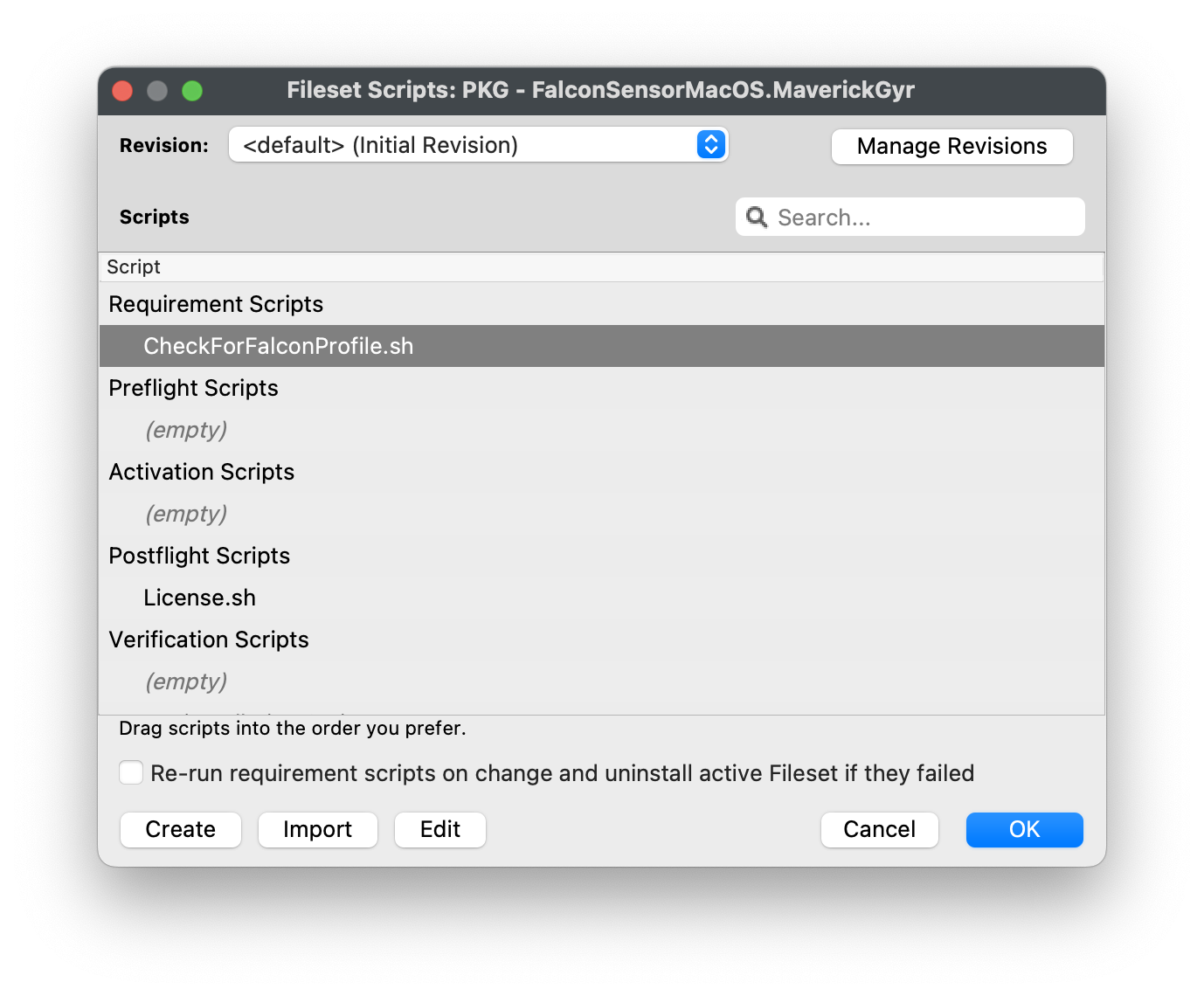](https://kb.filewave.com/uploads/images/gallery/2023-08/0gNEhaHHCGjdxqfl-checkforfalconprofile1.png) |
| #### Entering in your Payload Profile Identifiers 1. Highlight the string after profile\_id="#####" 2. Replace the ######, with your TCC profile Identifier. 3. If not sure, open your Profile and copy the Identifier. 4. Click OK to save 5. Click OK to save again to save your changes to the CrowdStrike Fileset | [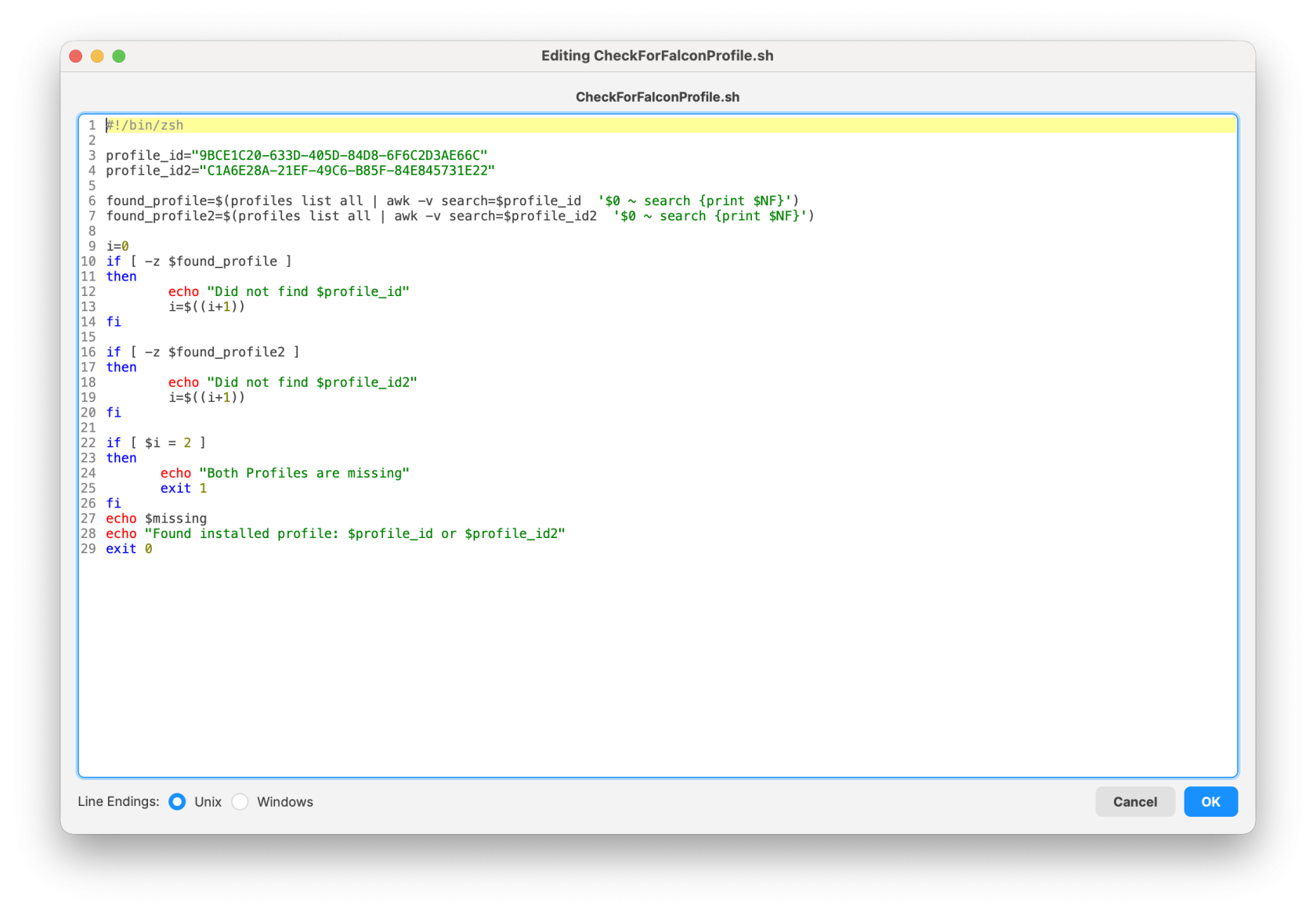](https://kb.filewave.com/uploads/images/gallery/2026-01/Xz4IRMby3JgnHeWn-screenshot-2026-01-30-at-17-46-23.png)
Check for Falcon profile script``` #!/bin/zsh profile_id="9BCE1C20-633D-405D-84D8-6F6C2D3AE66C" profile_id2="C1A6E28A-21EF-49C6-B85F-84E845731E22" found_profile=$(profiles list all | awk -v search=$profile_id '$0 ~ search {print $NF}') found_profile2=$(profiles list all | awk -v search=$profile_id2 '$0 ~ search {print $NF}') i=0 if [ -z $found_profile ] then echo "Did not find $profile_id" i=$((i+1)) fi if [ -z $found_profile2 ] then echo "Did not find $profile_id2" i=$((i+1)) fi if [ $i = 2 ] then echo "Both Profiles are missing" exit 1 fi echo $missing echo "Found installed profile: $profile_id or $profile_id2" exit 0 ``` |
| **Sensor State** | **Output Value** |
| Installed | Installed | version\_number |
| Not Installed | Not Installed |